What is NetSuite Application and Operational Security?
NetSuite application and operational security blocks unauthorized network and service connections while allowing customers convenient access to NetSuite from anywhere, with complete confidence. Security starts with strong encryption, role-based access controls, and robust password policies. NetSuite adds layers of additional protection, including multi-factor end-user authentication, and token-based application authentication. NetSuite’s round-the-clock monitoring and dedicated and tenured security team—backed by advanced tools, controls and policies—ensures the strongest operational data center security.
How NetSuite Works With You to Secure & Manage Your Data (Video)
Confidently access NetSuite from anywhere

Robust Foundation for Compliance
Oracle NetSuite has the certifications, tools, and advisory services to help you meet your regulatory, operational and compliance challenges. Credit card and personally identifiable information is always secure, and NetSuite is externally audited to SOC 1 Type 2 and SOC 2 Type 2 (SSAE18 and ISAE 3402) standards while maintaining ISO 27001 and 27018, PCI DSS and PA-DSS compliance.
The company could have handled the growth without an ERP system, but we would have been forced to hire a lot more people.
Learn How ERP Can Streamline Your Business
Free Product Tour(opens in new tab)
NetSuite Application and Security Benefits
NetSuite Application and Operational Security Features
NetSuite application and operational security is focused on protecting your data, services, and network via industry-leading controls, certifications, and privacy.
Encryption
Transmission of user credentials, as well as all data exchanged, are encrypted with an industry-standard protocol and cipher suite. NetSuite supports custom attribute encryption and provides encryption APIs. NetSuite uses token-based application authentication and multi-factor end-user authentication (MFA).
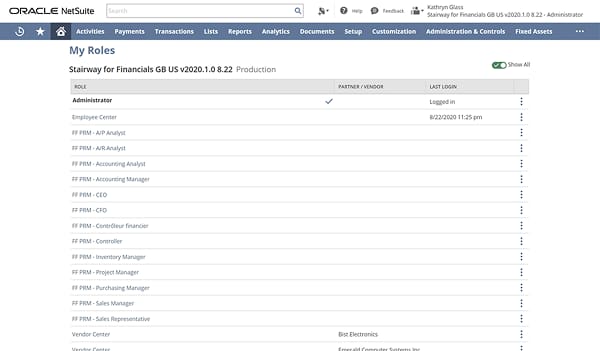
Role-Level Access
End users can be assigned roles with specific permissions and restrictions to see only the data, and use only the features, required for their jobs — right down to the field level. NetSuite provides a complete audit trail, tracking transactions by user login details and applying a timestamp to each change.
Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) is another layer of securing user access to your NetSuite account. In addition to a username and password, a role can be configured with an additional layer of protection where users provide a verification code. The verification code can be obtained from an authenticator app, or for example, by a message sent to a mobile phone.
Password Policies
Customers have granular password configuration options, ranging from the length of the passwords to the password expiration policy. They can set up strict rules to ensure that new passwords vary from prior passwords and that passwords are complex enough to include a combination of numbers, letters and special characters. In addition, accounts are locked out after several unsuccessful attempts.
Continuous Monitoring
NetSuite employs both network- and server-based Intrusion Detection Systems (IDSs) to identify malicious traffic attempting to access its systems. Security alerts and logs are sent to a security information and event management (SIEM) system for monitoring, and response actions, when required, are executed by an experienced, in-house security team.
Separation of Duties
In addition to mandatory employee background checks at all levels of the organization, Oracle NetSuite follows the Principle of Least Authority (POLA) — employees are given only those privileges necessary to do their jobs.
Dedicated Security Team
Oracle NetSuite employs a global security team dedicated to enforcing security policies, monitoring alerts and investigating any anomalous system behavior, including unauthorized connection attempts and malicious software. Near-real-time monitoring is in place with a 24x7 worldwide incident response capability. All access to production systems is approved and regularly reviewed by the security team.
Performance Audits
Oracle NetSuite implements auditing controls appropriate for SOC 1 Type II, SOC 2 Type II, ISO 27001 and PCI compliance, and employs a comprehensive risk management process modeled after the National Institute of Standards and Technology’s (NIST) special publication 800-30 and the ISO 27000 series of standards. Periodic audits ensure that personnel performance, procedural compliance, equipment serviceability, updated authorization records and key inventory rounds meet or exceed industry standards.
Security Certifications
Oracle NetSuite issues reports upon the completion of periodic SOC 1 Type II and SOC 2 Type II audits and is certified for PCI DSS and ISO 27001:2013.
- Oracle NetSuite has defined its information security management system in accordance with NIST 800-53 and ISO 27000 series standards.
- Oracle NetSuite’s SOC 1 Type II and SOC 2 Type II audits are prepared and audited by independent third-party auditors. A SOC 1 Type II audit is essential to meeting the reporting requirements of Section 404 of Sarbanes-Oxley relating to the effectiveness of internal controls for financial reporting. A SOC 2 Type II audit reports on controls that directly relate to the security, availability and confidentiality of services organizations.
- The PCI DSS security standard is designed to ensure that companies process, store and transmit payment card information in a secure environment. Oracle NetSuite’s Attestation of Compliance (AOC) is prepared and issued by a PCI Qualified Security Assessor (QSA).
- The Texas Risk and Authorization Management Program (TX-RAMP) provides a standardized approach for security assessment, authorization, and continuous monitoring of cloud computing services that process, store, or transmit the data of a Texas state agency. Oracle NetSuite has a Level 1 certification status for this program.
Privacy Certifications
Oracle NetSuite performs reviews and annual audits, conducts privacy risk management and oversees remediations, oversees privacy by design in technology and processes has a third-party vendor management program to ensure that the suppliers adhere to the privacy regulations, and is committed to maintaining and improving its privacy information management and data protection programs. Oracle NetSuite also provides Product Feature Guidance documents that describe how the service functionality is designed to assist customers with their privacy requirements.
- Oracle NetSuite has extended the ISO 27001 Information Security Management System to include the ISO 27018 control set, demonstrating protection and adequacy for processing Personal Information as a Public Cloud Hosting Provider.
- Oracle NetSuite’s adherence to the EU Cloud Code of Conduct (CoC) has been verified (Verification ID: 2021LVL02SCOPE218) and published on the monitoring body’s public registry(opens in a new tab). The CoC has been designed to define general requirements for cloud service providers as processor, demonstrating sufficient guarantees under Art. 28.1-4 of EU General Data Protection Regulation (GDPR).
- Oracle Corporate (Oracle EMEA Ltd) has obtained EU/EEA-wide authorization from the European data protection authorities for its Binding Corporate Rules for Processors (“BCR-p”). This helps our customers address their privacy and security requirements under GDPR and other European data protection laws and regulations in the EU/EEA, the UK and Switzerland (“European Data Protection Law”). See the Privacy Code for Processing Personal Information of Customer Individuals (Oracle Processor Code)(opens in new tab).
Resources

Data Sheets
Access specifications, features and benefits of NetSuite infrastructure.